In a recent discussion with our IT team, we uncover answers to pressing questions during this time when companies are transitioning to more remote staff.
Working remotely has become a standard component for companies, these days especially. While there are many benefits of a remote work situation (more family time, flexible schedules more productivity, etc.), it's crucial to establish the right environment to help employees stay productive, enable them to feel connected with other co-workers, and help keep employees work secure.
It’s important to keep in mind the massive inherent security risk in everything we do digitally.
With the current prevalence of employees working from home, cybersecurity has become even more important for remote workers. Not only do employees risk a personal data breach, but proprietary company information is also more vulnerable.
Here are some best practices to make transitioning to a remote work environment as seamless and secure as possible.
Check-In With the IT Team
The first step is nailing the infrastructure. As CEO or business owner, meet with your IT team to discuss what is needed: how many employees will be remote, what you expect from employees, and security concerns. Provide the IT team with time to develop a secure plan and the resources to gather what’s required.
It's very important for employees transitioning from the office beginning remote work, to check in with the IT team. The IT team is ultimately going to have a remote system and certain procedures in place that allow for people to leave a network and still access the things that they need. Encourage employees to ask questions such as:
- Do I need to change my passwords?
- Do I need any extra equipment?
- Will I be able to access my accounts?
The IT team should have the answers to these questions and procedures outlined to transition the employee successfully. They may have extra equipment or know the extra steps that a remote worker needs to take to create a seamless and secure workspace.
Example: At GrowthForce, before any employee begins to work remotely, they have to set up multi-factor authentication for several different services.
Your IT team should provide the steps to take, any devices that are needed, and set up employees so that they’re secure and ready to go.
Two types of remote devices
There are two types of remote devices for remote employees: a Managed Device and BYOD (Bring Your Own Device).
Remote Work On Managed Device:
The best thing a company can do is to provide their remote worker with a managed device. A managed device is a device that is purchased by the company and used remotely by the employee.
This makes it easier for the IT team to manage security requirements on that device. It’s easier for IT to impose security requirements on a company-owned device, making it better for both the business and the employees.
If a company is able to manage the device on the backend, there are various services for IT teams that allow managed devices to follow certain policies (security policies, access policies) that can be implemented on remote devices.
BYOD: Bring Your Own Device
A BYOD approach is when companies allow remote employees to use their own devices (laptop, phone, etc.) Although this is a cheaper option, it comes with more security risks, as you are unable to look at the devices and determine whether they fall within security requirements.
Although a managed device is strongly encouraged, there are still ways to minimize risk on an employee's personal device.
Cyber Security
There are still basic measures you can take (regardless if it’s a managed device or BYOD) that will help minimize security vulnerabilities.
Require multi-factor authentication. Enabling this reduces your security liability significantly. This is a small step that most online services have, for example, Microsoft, Google, Apple, and bank accounts to name a few.
Mandate anti-virus software. Regardless of what computer your employees are using, make sure they have an anti-virus running. Even Macs can be susceptible to malware. Windows 10 has a built-in anti-virus that should be enabled by default. If they have another anti-virus installed (such as Norton, Webroot, or McAfee) make sure it is enabled and real-time protection is turned on.
Lock laptops. Remind employees to close and secure their laptops before moving away from it. Suggest setting shorter timeframes for lock screens, log-off, or even just a habit of putting it away to prevent access. Heed this guideline especially if employees are working in a public place, such as a coffee shop or park.
Before an employee works remotely, they must do this.
Check their internet connection!
As simple as this sounds, it is often overlooked and can create a lot of problems. The remote worker needs to have a good internet connection. Because everything is cloud-connected, if an employee has an inconsistent internet connection or a poor speed, it is a massive hindrance. Everything you do, accessing files, text chat, video calls, will all be affected by a bad internet connection.
An easy test is going to google, and searching for “speed test”. A widget comes up with a blue button that says “run speed test”.
Check with their IT team, but generally, people are going to want between 20-50 MPS as a minimum for their connection.
Keeping Open Communication: Video and Chat
Stay connected with your IT team. It is important to get issues fixed before they become bigger problems.
Communication is key. We recommend making sure employees have an easy way to communicate internally with team members on both video and instant text chat features. This is an easy way to make sure everyone is staying connected and for bridging the gap to feel more connected with their team. This helps instill a productive work environment.
Platforms like Slack, Skype, and Microsoft Teams are great for real-time, text chat tools.
For companies that have Microsoft 365, Microsoft Team chat feature is free - including both the chat tool and videos. Being able to immediately connect with someone visually and audibly makes the transition to remote working more seamless and takes away the feeling of separation.
Zoom and Microsoft Teams have been taking the lead in video chat.
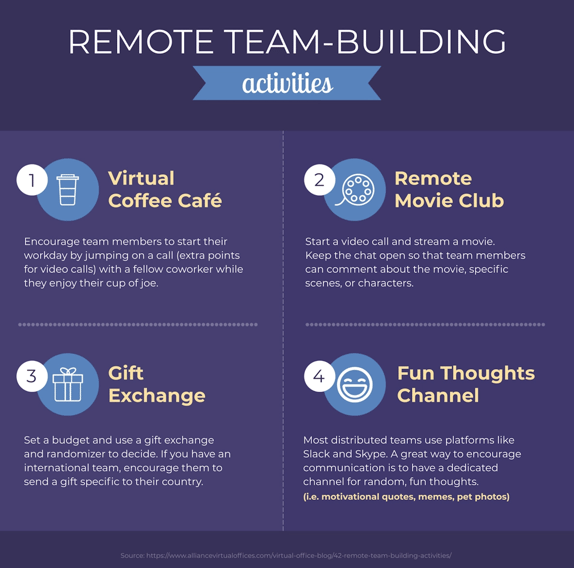
💡 Pro tip: Don't just use these platforms for work talk- make time for water cooler talks. Without these personal interactions, your company culture suffers. Employees will feel less connected to one another, which will ultimately make them feel less connected to your company- and your bottom line will take the hit. Here are some great ways for engaging employees remotely with virtual team-building activities...
Source: https://visme.co/blog/engaging-remote-employees/
Due Diligence
It comes down to making sure your IT team is up-to-date researching and learning about the safety practices of the newest devices and services being used.
IT should be looking at the security that each device company provides, and what security needs are in line with your company's guidelines.
Research and knowledge are key. We really never want to rely on the software and services we use for keeping us secure. It's up to your own technology team to create a safe working environment. Do your due diligence to make sure they're following the security protocols that you want and need.

.png?width=563&height=144&name=New%20GF%20Logo%20(37).png)